A new breach to investigate every month.
Examine the evidence. Piece together the clues. File your report. A free training drill from SignumCyber — because the best time to practice incident response is before you need it.
How it works
Read the brief
Understand what happened and who called you in.
Investigate
Click through areas to examine logs, emails, and digital evidence.
Build your case
Collect the critical evidence and rule out the dead ends.
File your report
Answer the key questions and get graded on your findings.
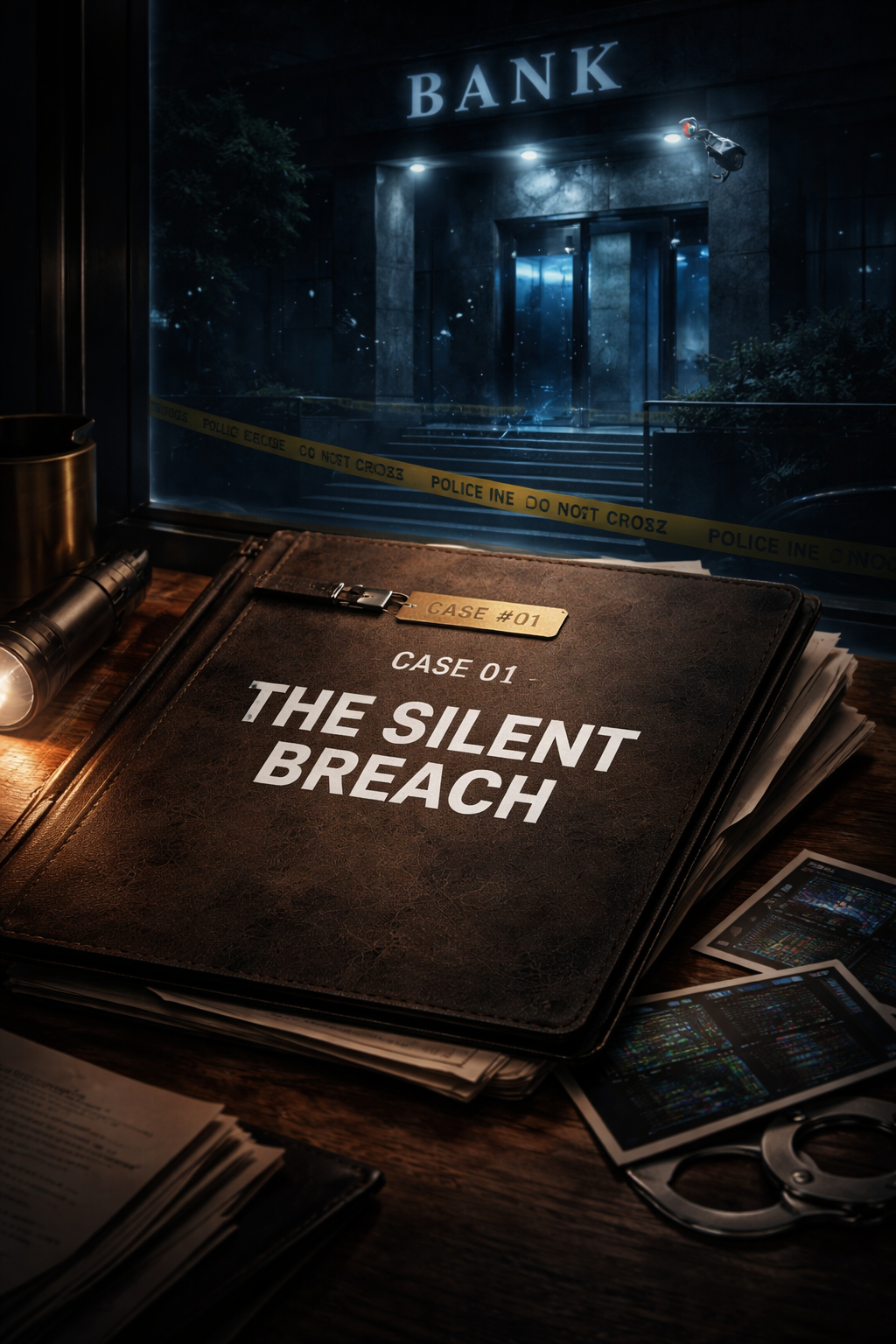
The Silent Breach
It is 7:02 AM on a Tuesday morning when your phone buzzes with an urgent alert from Meridian Financial Group. Their database monitoring system has flagged a massive spike in customer record queries during the early morning hours — far beyond anything their nightly batch processes would generate. The bank's CISO wants answers before the board meeting at noon. Twenty-three thousand customer records may have been accessed, and regulators will need to be notified within 72 hours if this is confirmed as a breach. The clock is ticking.
Next up
New cases drop on the 1st of each month. Here's what's on deck.
The Inside Job
Available May 2026The Ransomware Clock
Available June 2026This case is generic. Your risk isn't.
Free Case Files are generic scenarios — this month's is a financial-services firm; future months rotate through other industries. The SignumCyber platform builds Case File drills around your actual stack, vendors, people, and data, so your team practices responding to threats that reflect your real attack surface.
Get a custom Case File for your organization